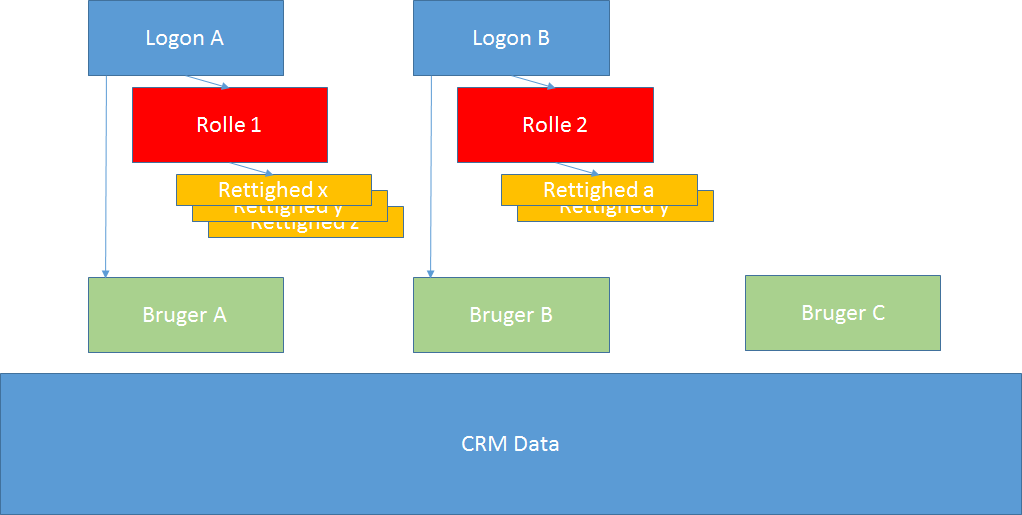
Access to ChannelCRM is granted to a user by a unique logon to the system. This way the system will always recognize the user and ensure that data and action are tracked to this user. The logon in combination with a strong password is also the mechanism ensuring that only you and your users have access to the system.
Each logon correspond to a "CRMuser". This is where additional information like contact information is stored.
A CRMuser can exist without a corresponding logon. As an example this will be the case for former employees. You will want to keep data, but the former employee should not be able to access the system.
CRMusers with no logon have no license cost.
Any logon should be granted a "Security Role". This could be "Administrator", "Consultant" or "Sales Management". From start you will find some typical security roles already in the system - but you can modify or build your own.
A Security Role contains several "Permissions" and maybe limitations. As an example the role "Sales Management" could have permissions to reassign Key Account Management for customers, whereas the role "Sales" cannot.
The security role "Administrator" is by default able to do anything.
The figure below is a visual representation of Logons, Roles and Users:
You can create new logons yourself, but only if you have a software license containing the total number of logons. Subscribtion.
To manage logons, users and security please use menu More../Setup/Logons. (You yourself will need to possess the security administrator role)
Here you will find a list of all logons and for each, when selected, the security role(s) assigned to the logon. In the example below the logon "Bente Fliid" is selected and we can see that she is granted the security role "Sales".
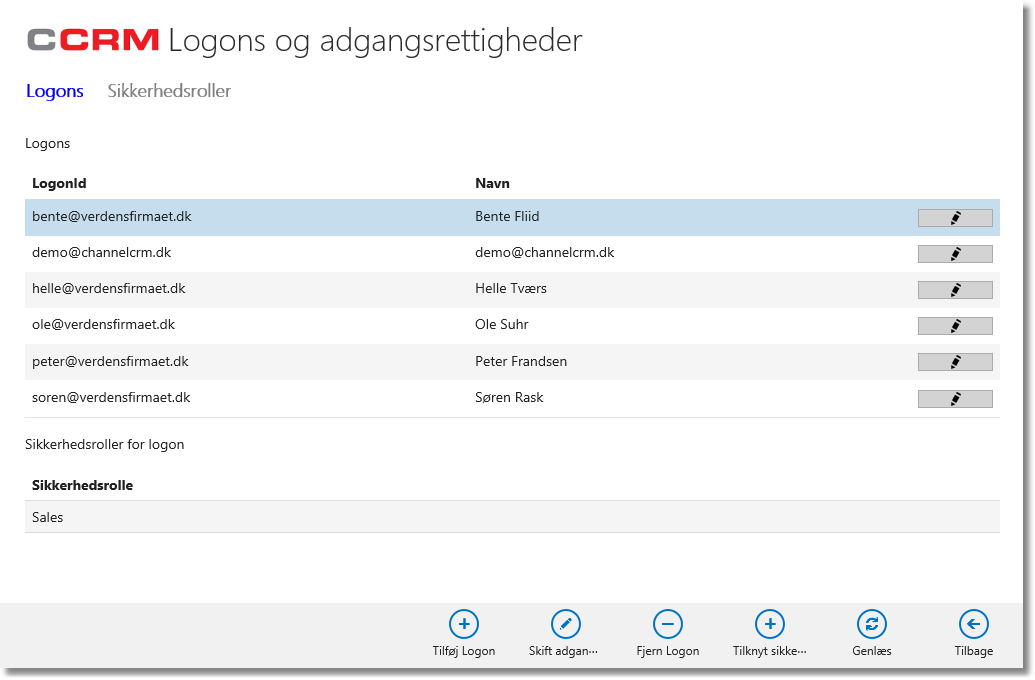
From the above screen you can create and delete logons. If a user is no more with the company - and as such should have no access - select the logon and click the button labelled "Remove logon".
To create a new logon (and user), click the button "Add logon":
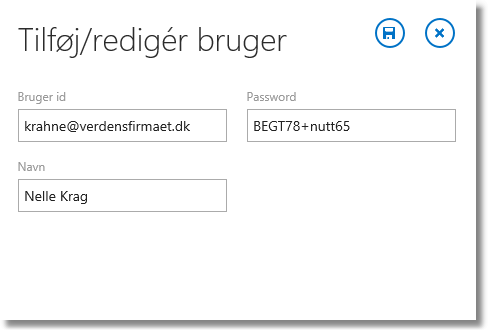
In the dialogue all three fields are to be entered:
•Iser ID: The e-mails address for the user.
•Password: Enter a password (7 or more characters, with at least one uppercase, one number and one special character)
•Name: The full name of the user.
Click "Save"
By now the logon as created but two things remains: More info on the user. And to grant a Security Role.
Information
Click the edit-button (pencil) in the logon row. This will open a dialogue in which you can enter additional information:
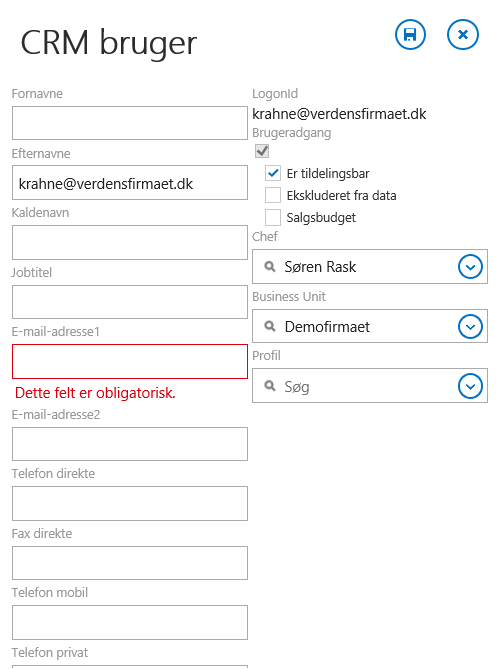
Fill in the fields as relevant. Especially the fields Firstnames, Lastnames and e-mail address1 are important.
The fields labelled "User Access", "Assignable" and "Excluded from data" bears special meanings:
•User Access: This will normally be checked. If you later on remove the logon for the user, the field will change into un-checked indicating that the user have no access.
•Assignable: Check this field if the user information are to be used actively in the system - like setting the user as KAM for a customer or like creating a meeting with the user participating. Normally you will leave this field checked.
•Excluded from data: This field is like a "soft delete" in the sense that the user will not show up in drop-down fields for assigning nor searching/filtering. The setting is mostly used for previous employees when all relevant entities (Companies, Contacts, Projects etc.) has been re-assigned to present employees.
Click Save. (Later on you can enter more complete data on the user - or the user can do so himself).
Security Roles
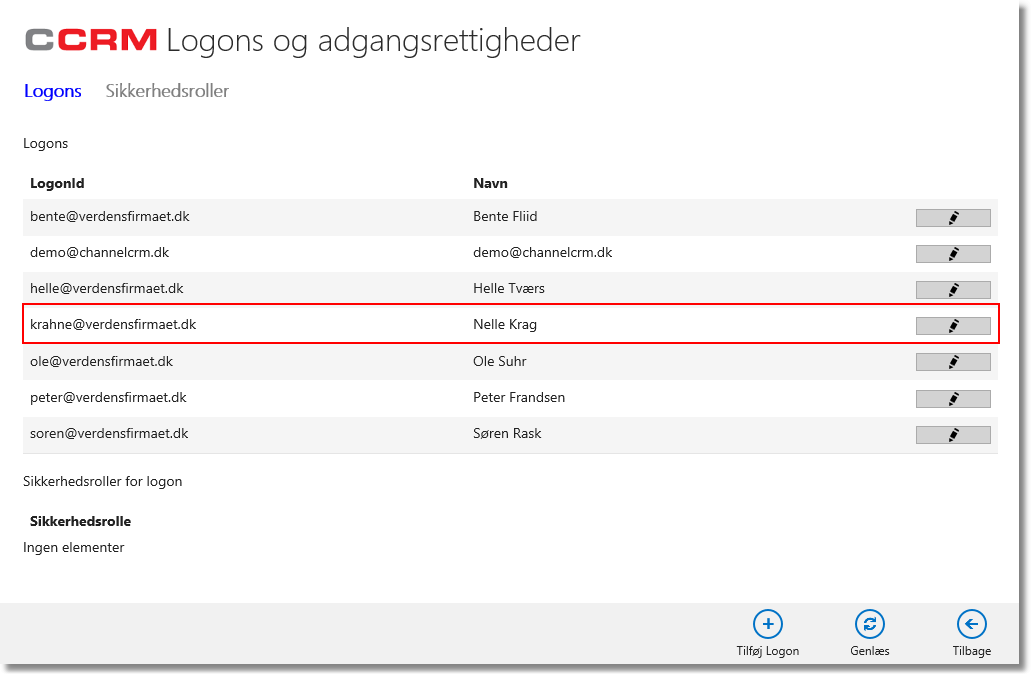
Back to the listing of logons you now select the newly added logon:
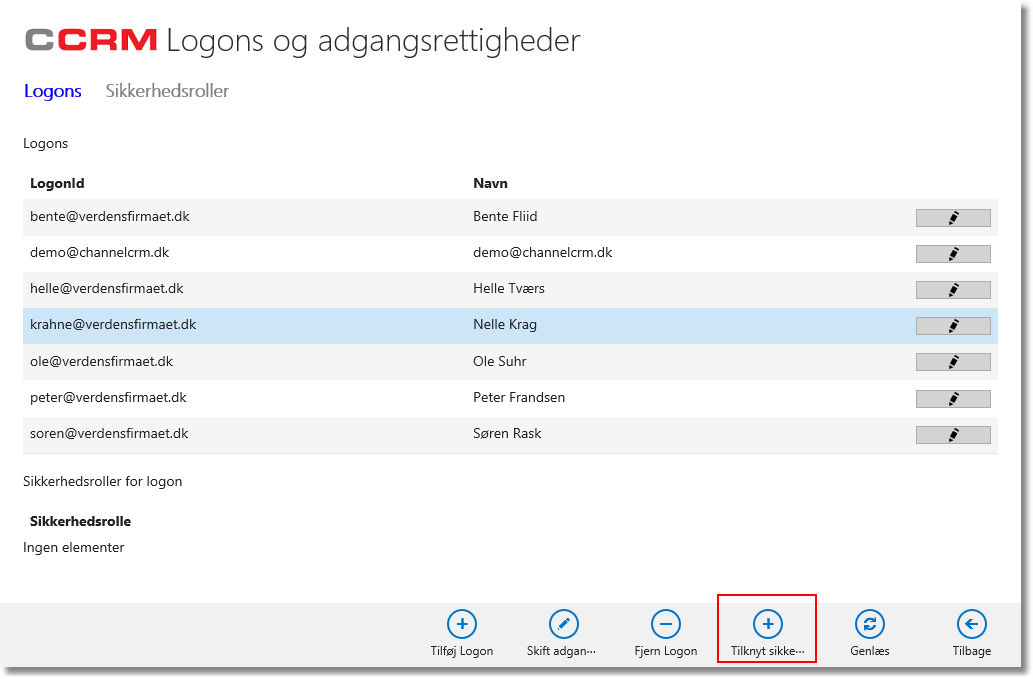
Click the button "Assign Security Role":
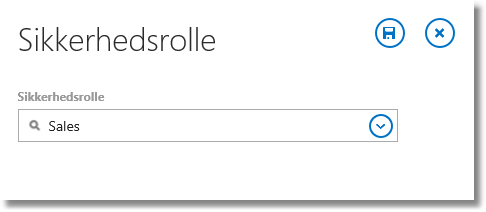
Select the role and click Save.
By now the user is created and he/she will be able to login to the system. First thing to do is to change the password.
More information on Security Roles.